
In this lab, you create machines using both the default network and a custom network that you create. You will explore how firewall rules work and see how you can communicate between machines running in different subnets in the same or different networks.
Google Cloud Platform's software defined networking allows you to create machines all over the world and treat them as if they were all on the same LAN. Machines in the same network can be physically located all over the world, but communicate via their internal IP addresses.
You also have the ability to create custom networks and subnets and have complete control over how machines communicate. This allows you to isolate machines for enhanced security.
By default, GCP blocks all IP ports. Firewall rules allow you to open ports and choose what machines have access to those ports.
What you need
To complete this lab, you need:
- The latest version of Google Chrome
- A Google Cloud Platform account and a project
What you learn
In this lab, you:
- Create a project
- Examine the default network created by GCP
- Create a second network
- Create and manage firewall rules
Step 1
Log onto the Google Cloud Platform web console at http://console.cloud.google.com.
Select a project to use for this lab, or create a new project now. If you don't know how to create a project, see the lab Getting Started with GCP.
Step 2
From the Products and Services menu  , choose VPC Network from the Networking section.
, choose VPC Network from the Networking section.
Notice that the first time you enter this services in a new project, a message will appear saying that Compute Engine is getting ready. At this point, the default network is being created. It will take a minute or so for this to complete.
Step 3
Once the initial network is setup, notice there are a number of subnets created, one for each region that supports Compute Engine.
Notice each subnet has an internal IP address range beginning with 10.
Step 4
Click Firewall rules from the navigation pane on the left. Notice that a number of rules have been created for you. The rule default-allow-icmp allows machines to ping each other. The rule default-allow-internal allows machines internal to this network to communicate via any port. There are also rules for ssh and rdp. These allow us to remotely connect to Linux and Windows machines respectively.
Step 5
From the Products and Services menu, choose Compute Engine. Click the Create button. On the Create an instance form, name the instance test-machine-1. From the zones dropdown, select any zone in us-central1.
Leave everything else as the default and click the Create button.
Step 6
When a green check appears next to the instance, click the SSH button to connect to it. Be aware that your browser's popup blocker might block the SSH window. If it does, just click the SSH button again and you also might have to approve the popup.
Once the connection is made, a Linux shell will appear. Type the command below.
ip addr show
It should display the network adapters and the IP addresses assigned. You should see a loopback adapter with a 127.0.0.1 IP and an ethernet adapter with an IP that starts with 10.
Step 7
Leave the SSH window open and go back to the console.
Create another instance. This time name it web-server. Select any zone in us-east1.
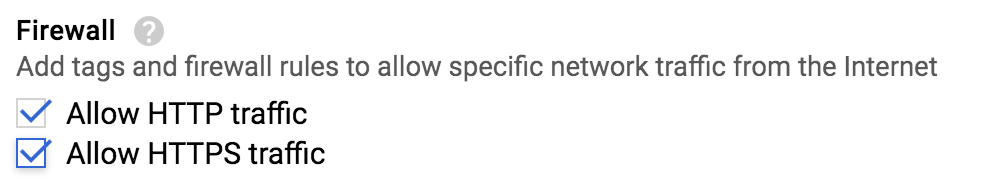
Scroll down to the Firewall section and check both allow HTTP and HTTPS traffic as shown below.
Leave everything else as the default and click the Create button.
Step 8
SSH into this machine like you did the first, and then enter the following command to install Apache Web Server.
sudo apt-get install -y apache2
Step 9
When the command completes, return to the web console and click the web-server machine's External IP address. Notice it fails. This is because you enabled HTTPS on the firewall rule and that is what it is using.
Change the request to HTTP instead. This time it will show the Apache default home page.
Step 10
Go back to the web console. Make note of both machines' internal and external IP addresses. Go to the SSH window of the test server. Try to ping the web server on the Internal IP. Just type the following (the IP address may be different):
ping 10.142.0.2
It should work. You are communicating between two machines in different data centers via their internal address!
Step 11
Press Ctrl+C on your keyboard to stop the ping command. Now ping the web server machine's external IP address.
It should work as well. Again, press Ctrl+C to stop the command.
Step 12
Go back to the web console and return to the VPC Network service. Click Firewall rules as you did earlier. Notice two additional rules were created for HTTP and HTTPS. These were created automatically when you created the web server earlier.
Step 13
Click the rule default-allow-http to see its details. Notice the target tag value of http-server. Recall when you checked the two checkboxes when creating the web server. This added these tags to that server. This firewall rule only applies to machines that have that tag.
This allows you to create rules that only apply to certain machines, not all the machines in a network.
Step 1
In the web console, return to the VPC Network service. Then click the Create VPC Network button at the top.
Step 2
Name your new network network-2.
Notice in the Subnetworks section you can manually create as many subnets as you want and you have control over the IP address ranges.
Click the Automatic tab. When you choose this, the subnets are created for you.
Scroll down and check the select all checkbox for the firewall rules.
Click the Create button to create the new network.
Step 3
Go back to the Compute Engine service. Click the Create Instance button. Name this instance test-network-2. Choose any zone you like to put this instance.
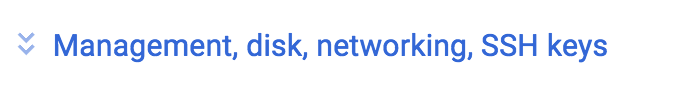
Scroll down and click the link shown below.
Click the Networking tab, click the edit button (pencil icon), then select your second network from the network dropdown. Click the Done button at the bottom of the Network interfaces section.
Click the Create button to create the machine.
Step 4
When the machine is created, SSH into it. Try to ping the other machines by their internal and external IP addresses.
Step 5
Create some additional machines and experiment with the various network settings.
Step 1
In the Compute Engine service, select all your running machines and click the Delete button. Verify that they all get deleted to ensure you are no longer paying for them.
Step 2
Go to the VPC Network service. Click the link to network-2 to see its details. Then click the Delete Network button at the top to delete it.

This lab was provided by ROI Training.
To learn more about GCP infrastructure check out the course: Architecting with Google Cloud Platform: Infrastructure.
Check out some related courses:
Please click the link below and give us some feedback on this lab. You will automatically be entered to win a new Google Home.
